Cyber security incidents seem to be happening with increasing frequency. Almost daily, some of the world’s largest and most successful companies are being breached. Huge corporations, such as eBay, Myspace, Anthem and Target, have suffered significant damages from security breaches. The culprit? Cyber hacking.
How?
At first thought, you may wonder how some of these hacks are possible. After all, overtly successful organizations often have the best IT-based security measures that money has to buy. What many people fail to realize is that electronic deficiencies are sometimes not associated with major breaches. Instead, the issue can be a company component that is common to every organization—people.
A primary source of cyber security failures is human error. People who have not received adequate training can become security liabilities for any company, regardless of its size or net worth.
Isn’t annual training enough?
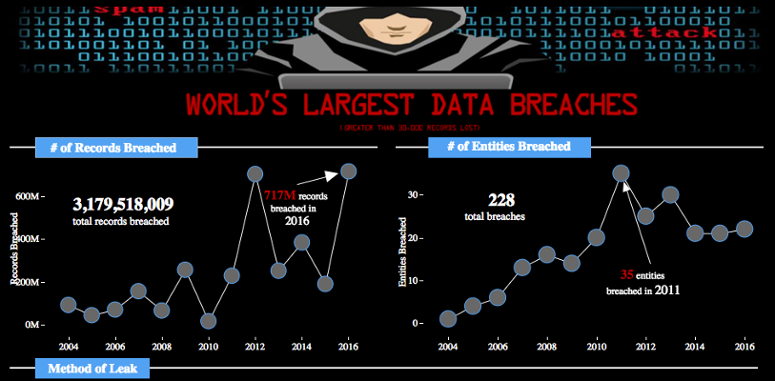
Companies may purchase the most expensive electronic security features and still fail at ensuring that their people are thoroughly prepared for a hacking attempt. Although many organizations have annual training in place, based on the number of cyber breaches that have occurred in recent years, the training has been insufficient. Tyler Cohen-Wood, an expert on cyber security who previously served as the Lead Senior Computer Forensic Examiner for the Department of Defense Cyber Crime Center, states, “In the past two years, we have seen a massive upswing in hackers breaking into some of the most highly secure corporations and stealing financial data, intellectual property, and very sensitive personal information—and it seems to be growing exponentially.”
In some cases, the number of records accessed during a cyber breach is difficult to fathom. For instance, according to Tableau Public’s Chart of the World’s Largest Data Breaches, the Myspace hack resulted in 164 million records being breached by cyber criminals. Similarly, 145 million eBay records were accessed, and Anthem suffered a breach of 80 million. These numbers represent detailed personal information being shared with criminals attempting to steal money through identity theft. A single breach can be financially significant to a company not only because of the money needed to restore normal operations and cover immediate damages, but also because of the loss of consumer confidence in the organization’s brand. IBM’s 2019 Cost of Data Breach Study: Global Analysis indicates that on average, a company in the U.S. can expect to pay approximately $8.64 million for a single breach.
Annual training often focuses on the basics of cyber security, but is generally designed to cover a large amount of information in a short period of time. As a result, company workers may not retain the crammed data, and employees’ names on the classroom roll may not really confirm that they are prepared for the cyber attacks laying wait in their emails.
Since company workers often use personal devices as well as company computers to access emails and perform their work, there are multiple opportunities for cyber breaches to occur through uninformed choices. A clicked link or slip of the tongue could inadvertently disclose protected information, and once the information is shared, it cannot be retrieved.
Effective Training
Nowadays, more effective training techniques have been developed to help employees better retain crucial information that can help avert a cyber breach. Newer approaches include the dissemination of information to company workers through frequent, small training sessions. The smaller sessions help employees stay focused throughout their cyber training, and the frequency of the training keeps the information fresh on the workers’ minds.
In order for training to be effective, its results must also be measurable. Proper training should include evidence-gathering methods to confirm that employees actually understand their training and are prepared for possible cyber attacks.
Companies should keep in mind is that their electronic security measures are simply not enough to avoid a cyber breach. Their people are their strongest and weakest defense against cyber incidents.